CVE-2021-34527|微软发布打印机漏洞补丁 火绒工程师提醒用户尽快修复
-
作者:火绒安全
-
发布时间:2021-07-07
-
阅读量:6323
7月1日,微软发布了一个存在于Windows打印服务( Windows Print Spooler)的高危漏洞,CVE-2021-34527。该漏洞EXP已经在外网公开,并且被攻击工具收录,有很大可能被利用。7月7日,微软对该漏洞发布补丁,火绒产品(个人版、企业版)已进行紧急升级,用户可以使用【漏洞修复】功能进行修复。
1、漏洞详情
Windows Print Spooler 蠕虫级远程代码执行0day漏洞 CVE-2021-34527
CVSS:8.8
严重级别:危急
被利用级别:检测到利用
Windows Print Spooler是Windows的打印机后台处理程序,利用该漏洞,攻击者可以使用一个低权限用户(包括guest用户),对域控发起攻击,进而控制整个内网。
2、修复建议:
1、通过火绒个人版/企业版【漏洞修复】功能修复漏洞。
个人用户在可以在软件“安全工具”中,下载“漏洞修复”工具,点击“开始扫描”即可。
企业用户管理员可通过“控制中心”-“漏洞修复”派发策略,统一扫描、修复终端漏洞。
2、下载并安装微软官方补丁
https://msrc.microsoft.com/update-guide/en-US/vulnerability/CVE-2021-34527
3、不方便打补丁的用户,可使用微软给出的缓解措施:
选项 1 - 禁用 Print Spooler 服务
如果禁用 Print Spooler 服务适合您的企业,请使用以下 PowerShell 命令:
►Stop-Service -Name Spooler -Force
►Set-Service -Name Spooler -StartupType Disabled
影响:禁用 Print Spooler 服务会禁用本地和远程打印功能。
选项 2 - 通过组策略禁用入站远程打印
您还可以通过组策略配置设置,如下所示:
►计算机配置/管理模板/打印机
►禁用“允许打印后台处理程序接受客户端连接“:策略以阻止远程攻击。
影响:此策略将通过阻止入站远程打印操作来阻止远程攻击媒介。该系统将不再用作打印服务器,但仍然可以本地打印到直接连接的设备。
3、影响范围:
- Windows Server 2012 R2 (Server Core installation)
- Windows Server 2012 R2
- Windows Server 2012 (Server Core installation)
- Windows Server 2012
- Windows Server 2008 R2 for x64-based Systems Service Pack 1 (Server Core installation)
- Windows Server 2008 R2 for x64-based Systems Service Pack 1
- Windows Server 2008 for x64-based Systems Service Pack 2 (Server Core installation)
- Windows Server 2008 for x64-based Systems Service Pack 2
- Windows Server 2008 for 32-bit Systems Service Pack 2 (Server Core installation)
- Windows Server 2008 for 32-bit Systems Service Pack 2
- Windows RT 8.1
- Windows 8.1 for x64-based systems
- Windows 8.1 for 32-bit systems
- Windows 7 for x64-based Systems Service Pack 1
- Windows 7 for 32-bit Systems Service Pack 1
- Windows Server 2016 (Server Core installation)
- Windows Server 2016
- Windows 10 Version 1607 for x64-based Systems
- Windows 10 Version 1607 for 32-bit Systems
- Windows 10 for x64-based Systems
- Windows 10 for 32-bit Systems
- Windows Server, version 20H2 (Server Core Installation)
- Windows 10 Version 20H2 for ARM64-based Systems
- Windows 10 Version 20H2 for 32-bit Systems
- Windows 10 Version 20H2 for x64-based Systems
- Windows Server, version 2004 (Server Core installation)
- Windows 10 Version 2004 for x64-based Systems
- Windows 10 Version 2004 for ARM64-based Systems
- Windows 10 Version 2004 for 32-bit Systems
- Windows 10 Version 21H1 for 32-bit Systems
- Windows 10 Version 21H1 for ARM64-based Systems
- Windows 10 Version 21H1 for x64-based Systems
- Windows Server, version 1909 (Server Core installation)
- Windows 10 Version 1909 for ARM64-based Systems
- Windows 10 Version 1909 for x64-based Systems
- Windows 10 Version 1909 for 32-bit Systems
- Windows Server 2019 (Server Core installation)
- Windows Server 2019
- Windows 10 Version 1809 for ARM64-based Systems
- Windows 10 Version 1809 for x64-based Systems
- Windows 10 Version 1809 for 32-bit Systems
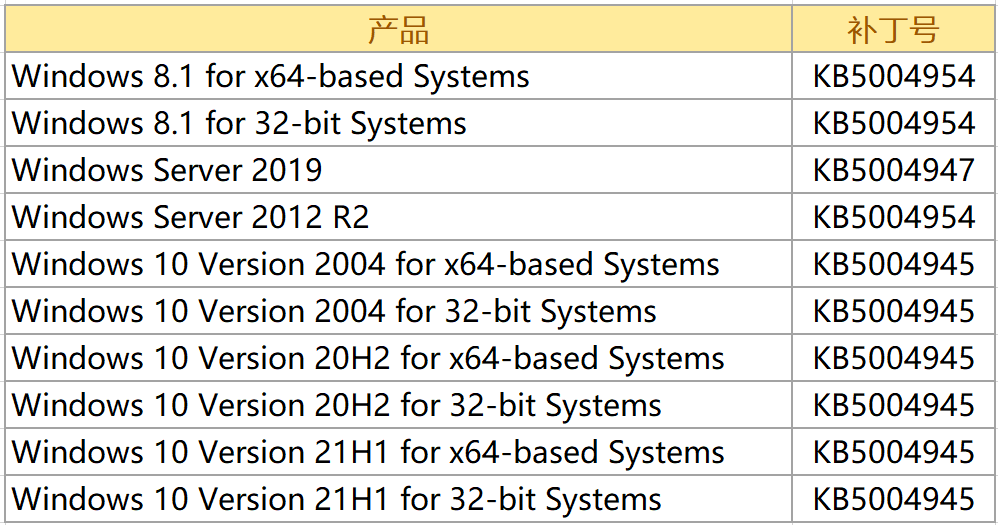
注意,微软本次并未对所有受影响系统进行修复,以下系统更新将延迟发布:
- Windows Server 2012 (Server Core installation)
- Windows Server 2012
- Windows Server 2016 (Server Core installation)
- Windows Server 2016
- Windows 10 Version 1607 for x64-based Systems
- Windows 10 Version 1607 for 32-bit Systems
相关内容:
《Windows 打印服务风险通告(CVE-2021-34527)》
《CVE-2021-1675(Windows Print Spooler 远程命令执行漏洞)漏洞通告 | PoC公开》
微软官方通告:
https://msrc.microsoft.com/update-guide/en-US/vulnerability/CVE-2021-34527